In a bid to evaluate the factors that contribute to better and secure user experience, the first panel saw an insightful discussion on the best practices in the industry and the ways to build a sturdy backend and network along with optimum security mechanisms in the gaming sector.
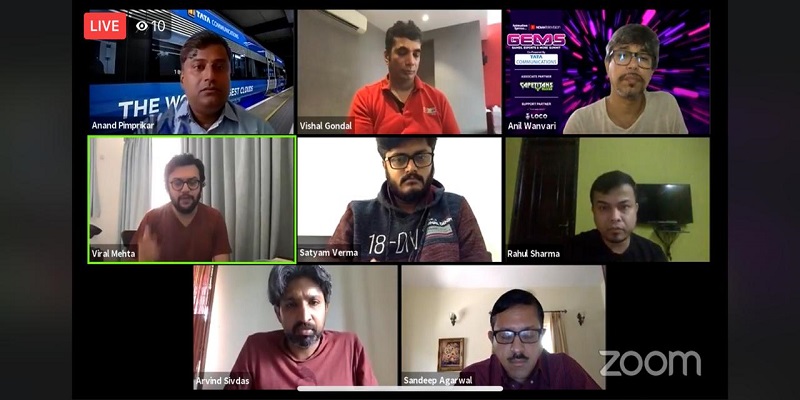
Panelists included Tata Communications head of sales BD – India Media & Entertainment services Anand Pimprikar, Supercric co-founder and CEO Arvind Sivdas, Winzo lead backend developer Rahul Sharma, Games24X7 chief technology officer Sandeep Agarwal, PAYTM First Games chief operating officer Sudhanshu Gupta, Pocket52 co-founder and chief technology officer Satyam Verma, LOCO-Pocket Aces VP Engineering Viral Mehta, GOQII founder and CEO and nCore Games founder Vishal Gondal.
A secure and reliable network is crucial in esports, where milliseconds can be the difference between winning and losing. Throw in 4K streams and the recent explosion of augmented and virtual gaming (AR/VR), and networks are often pushed past their limits – much to the dismay of gamers who have brought the term ‘gamer rage’ into the mainstream. Then take the latest mega-trend of mobile gaming which is extremely popular in India.
Discussing how crucial is the network to the industry and how is software changing the gaming world, Gondal explains, “I think the question of user experience is very important because now consumers are experiencing the best apps in the world. If you’re from India, you’re using Uber, you’re using Amazon, you’re playing Clash Royale, Clash Of Clans, PUBG and Fortnite. Bottomline is that consumers have already tasted these apps and the experience that they provide and if you’re going to be anywhere inferior to that then the consumers are going to reject it.”
According to Gondal, this is not limited to gaming alone, this is happening across categories. “Homegrown applications are no longer competing with the Indian apps or the apps in their region but they are competing with the best in the world,” he shares.
While maintaining a seamless user experience, developers have reported increasing amounts of cyber attacks ranging from hacking to DDOs to level seven to theft in real money gaming through OTPs.
Distributed denial of service (DDoS) attacks are one of the principal threats to content delivery network (CDN). Using malware to remotely control thousands of computers and direct them to overwhelm a specific target with bogus requests, CDN DDoS attacks cause a network to become slow or unavailable to users, potentially resulting in lasting damage to reputation, productivity and profitability.
Throwing light upon the issue, Agarwal shares that it is extremely critical to prevent DDOS attacks and ring-fence against third party attackers. He shares, “Not a day goes by when we don’t see a DDOS attack, it originates from a lot of different places in the world. The way we protect is with the bunch of software tools that we have. We do protection both at L3 and L4 levels and also at L7 levels. There is an open-source software hosted on a cloud source provider which helps us take care of that. At L7, we use firewalls from a couple of providers so that we continue to stay available for our users.”
On being asked how Sharma keeps abreast of the ways to deal with the attackers, he answers, “We keep analysing what sort of threat and attacks could come our way and the infrastructure we need to put in place in order to safeguard ourselves. We have third party services keeping those threats away. We have a team that keeps analysing those threats. It’s a continuous development.”
While the whole server site security risks are serious enough; according to Gondal, the bigger security threats we face are from other platforms like Twitter, Facebook and Instagram with the whole advent of fake apps and Id’s being sold. He shares, “500 fake Fau-G apps are already on google that we are trying to bring down. None of these platforms ever take this seriously. Several accounts on Twitter, Facebook Instagram are selling you fake ID’s. So there are a lot of these phishing apps who are using gaming as a front. And especially in real money gaming, it is a huge problem.”
Speaking about the possible solutions to the menace of attacks, Pimprikar shares, “We at Tata Communications have an integrated management where we look at extreme security incidents.” On being asked by Gondal if they could help them with the safeguards against fake apps, Pimprikar obligingly offered to have an offline chat to discuss their holistically-managed threat management and brand protection mechanisms.
While Verma shares attacks that are really sophisticated and read your patterns, he also feels we can protect ourselves by identifying the vulnerability in our service. He shares, “You yourself are the best judge of what your healthy traffic is. We have to identify that these are my healthy URLs and my patterns of traffic. And if something is crossing that, it goes into the bad cluster and then we can put restrictions. Like banning the IP’s and banning the floods. Sometimes like these days, there are a lot of bots available publicly. We can just go to the dark web and buy some botnets out there and do some proper distributed IPs attacks.”
Sivdas opines that it is important to err on the side of thinking through security at the early stages of product development. He shares, “If you think of security early on product development, it makes for a much easier approach. There is always this trade off when you’re making the product as to whether you should invest early or put the product out and we will put a blanket around it and that balance is a very tricky one.”
Examples of approaches range from bug bounty approach to honey pot approach. Verma feels it is a cat and mouse game ‘as to who is ready to put in more resources.’ Gondal highlights another menace that afflicts the scenario which is the problem of compliance of court orders.
Having personally experienced it, he shares that even with a court order, it is difficult to get social media giants to reveal the information about the hackers and thieves enjoy the benefits of anonymity.
While the US has laws such as the Patriot Act where platforms can be compelled to disclose personal information if asked by the court, the same can not be said about India. He shares, “The problem is that none of these social media networks are willing to give up these people’s identities despite court orders. Again we’re facing a similar issue. It is just that we’re learning this from experience. In our case, we had a court order and Facebook, Instagram and Twitter, in complete contempt of court, are not even following the court orders, they are not following the cyber police complaints. If you go to a housing society saying there is a Gunda (thug) living here, the housing society will tell you who this is but these platforms just refuse to comply. So at one end, they are making revenues from India, on the other, you are not even willing to comply.”
Panelists also discussed the ways in which developers can continue to ensure the best user experience. Verma opines that keeping applications lightweight is very important. He shares, “Serving things through CDN helps a lot and I think a major part is that you have to write some really good fall back mechanisms. Let’s say your user has a really good 4G network and he is travelling and keeps going from 2G to 3G to 4G, you need to have a really good fallback on your backend and client both. And you render less information on his screen when he is on a lower network to make sure the critical part is always there to give him the experience of playing.”
According to Agarwal, having a team that can optimise the performance keeping in mind all the factors can lead to better user experience. He shares, “Having a smarter engineering team that is cognisant of making the choice upfront before they go down a certain path and have to do a major course correction, separates a better team from not so good teams.”